Remove Activation Key Cisco Asa 5585
Adaptive Security Appliance FAQ - Cisco. Cisco ASA Software................................................................................. ASA Releases.................................................................................... Cisco ASAv Software............................................................................. Licensing.........................................................................................
Certifications..................................................................................... ASA Hardware...................................................................................... Physical Appliances............................................................................... Performance and Scalability.......................................................................
1 I celebrate myself, and sing myself, And what I assume you shall assume, For every atom belonging to me as good belongs to you. I loafe and invite my soul.
Advanced Protection............................................................................... Botnet Traffic Filter.............................................................................. Cisco IPS....................................................................................... Next- Generation Firewalls (CX)................................................................... Cloud Web Security Integration...................................................................
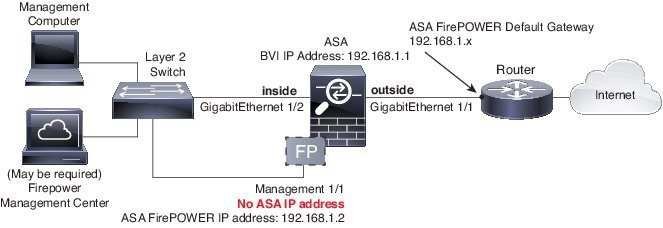
Management....................................................................................... Deployment Modes................................................................................. Routed Mode.................................................................................... Transparent Mode...............................................................................
Miscellaneous................................................................................... Access Control..................................................................................... Security Group Tags............................................................................. Protocol Inspection................................................................................. Network Address Translation.......................................................................
VPN............................................................................................... Cisco Any. Connect............................................................................... Clientless VPN.................................................................................. SSL Decryption.................................................................................. Miscellaneous................................................................................... High Availability.................................................................................... Failover.........................................................................................
Ordering........................................................................................... Q. What is Cisco. It offers stateful firewalling, VPN capabilities, and clustering capabilities; provides for the scalability of ASA hardware; and integrates with other security solutions like Cisco IPS, Cisco Cloud Web Security, Cisco Identity Services Engine (ISE), and Cisco Trust. Sec. . In addition, it offers next- generation firewall capabilities through the ASA CX software module on ASA5. X or through a Security Services Processor (SSP) in the ASA 5. X appliances. Cisco ASA Software is not forked off Cisco IOS. Its roots are in the Cisco Finesse.
It also supports mixed- route and transparent- mode multicontext configurations. Most important, with ASA Software. VPN resources can be flexibly allocated in a system context. Q. Where can I find guidelines on migrating from the Cisco Catalyst?
Then you have to edit the converted configuration to match that of an ASA 5. X. Q. What is the Cisco ASAv? The ASAv supports consistent, transparent security across physical, virtual, application- centric, and cloud environments. The policy rule is integrated into ASA policy and its stateful firewalling. The ASAv software does not do anything special to drop traffic that exceeds the threshold. If the v. CPU is running close to close to capacity, incremental traffic will see a drop in speed. Also keep in mind the underlying virtual switch capacity.
Combined Licenses in Failover and Clustering. Prior to Cisco ASA Software version 8.3(1), both units in a failover pair required identical licensed feature sets.
Q. What hypervisors does ASAv support? Note that ASAv is independent of the virtual switch and does not require Cisco Nexus 1. V. Temporary licenses are also known as demo licenses because they are commonly used for product or feature evaluation. In addition, ASAv comes in two flavors: namely, a one- v. CPU model and a four- v. CPU model. It supports these license tiers: ?
Cisco ASA Software is the core operating system that powers Cisco ASA firewall products. It offers stateful firewalling, VPN capabilities, and clustering capabilities. ASA 5585-X Adaptive Security Appliance: Access product specifications, documents, downloads, Visio stencils, product images, and community content.
It will ship preinstalled when ordered with the appliance. A license is exclusively tied to the serial number of the ASA appliance. It cannot be transferred. Starting with Release 8. Typically, you buy a license only for the primary unit; for active/standby failover, the secondary unit inherits the primary license when it becomes active. If you have licenses on both units, they combine into a single running failover Cluster license.
Cluster units do not require the same license on each unit. Typically, you buy a license only for the master unit; slave units inherit the master license. If you have licenses on multiple units, they combine into a single running ASA Cluster license. Both units in an ASA 5.
X through ASA 5. 55. X system require the IPS module license. You also need the IPS signature subscription on the IPS side for both units. See the following guidelines. Like other ASA licenses, the IPS module license is technically shared in the failover Cluster license. However, because of the IPS signature subscription requirements, you must buy a separate IPS module license for each unit. Frozen Throne Rexxar Campaign Download Youtube on this page. For ASAv CPU failover deployments, you must make sure that the standby unit has the same number of virtual CPUs assigned to it as the primary unit (along with matching v.
CPU licenses). Note: A valid permanent key is required; in rare instances, your authentication key can be removed. If your key consists of all zeros, then you need to reinstall a valid authentication key before failover can be enabled. Q. What are the licensing requirements for ASA clustering? A Cluster license is required on each unit. For other feature licenses, cluster units do not require the same license on each unit. If you have feature licenses on multiple units, they combine into a single running ASA Cluster license.
Note: Each unit must have the same encryption license and the same 1. GE I/O license. Cisco ASA 5. X Security Plus license supporting 2 units. Note: Each unit must have the same encryption license.
Cisco ASA 5. 51. 5- X, ASA 5. X, ASA 5. 54. 5- X, ASA 5. XBase license supporting 2 units.
Note: Each unit must have the same encryption license. All other models.
No support. Q. How do licenses combine for failover pairs or cluster units? If you buy separate licenses for each unit, then the combined license uses the following rules. For licenses that have numerical tiers, such as the number of sessions, the values from each unit’s licenses are combined up to the platform limit.
If all licenses in use are time- based, then the licenses count down simultaneously. Failover Examples. The licenses will be combined for a total of 2. Probleme Mit Adobe Reader Installation Files. Any. Connect Premium sessions. Because the platform limit is 7. Any. Connect Premium sessions. In the above example, if the Any.
Connect Premium licenses are time- based, you might want to disable one of the licenses so that you do not “waste” a 5. The combined license allows 3. For active/active failover, the contexts are divided between the two units. One unit can use 1. Clustering Examples. Because the platform limit is 1. Therefore, you can configure up to 1.
Because the platform limit is 2. Therefore, you can configure up to 1. Only licenses with a status of “enabled” are used. The duration of enabled time- based licenses that do not have numerical tiers is the combined duration of all licenses.