Checkpoint Ips Software Blade Download

How to check if a Security Gateway is covered by an Application Control Software Blade contract in User Center. How to check if a Security Gateway is covered by an Application Control Software Blade contract in User Center.
Collection News : 12-Sep-2014 The CheckPoint community releases a new collection of Visio shapes for CheckPoint products, and other supporting products. Check Point Full Disk Encryption Software Blade
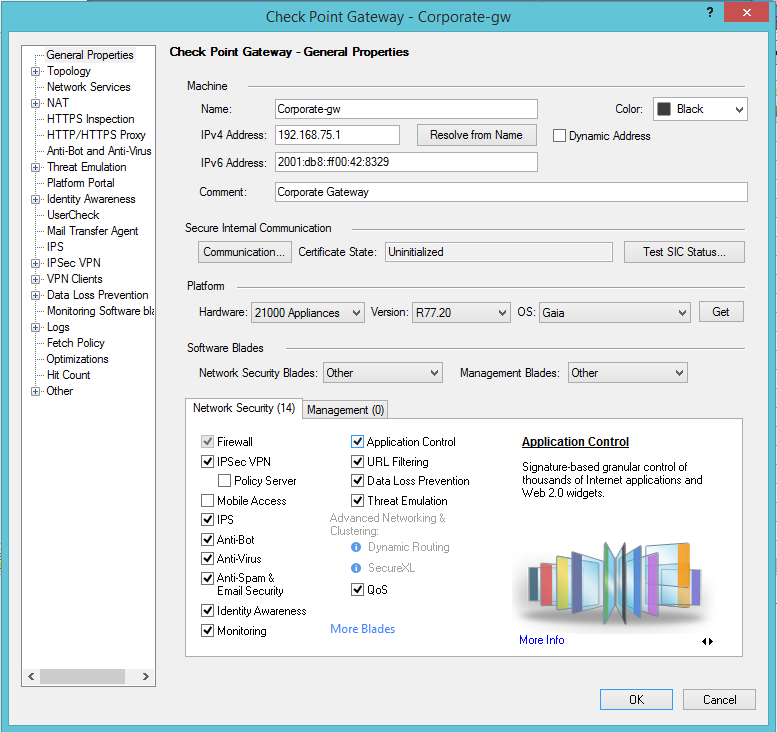
Table of Contents. Overview. Licensing and Contracts.
Cisco Intelligent WAN is the foundation for SD-WAN. Learn how this hybrid solution delivers simplicity and automation for your business at compelling cost.
Application Control Software Blade. How to verify the status of Application Control contracts in all your Security Gateways. Notifications about insufficient contract coverage.
What happens when there is no Application Control contract. New Installation or Upgrade of R7. When using Evaluation Contracts. Grace Period. FAQOverview. Licensing and Contracts.
Make sure that each gateway has a Security Gateway license and an Application Control contract. For clusters, make sure you have a contract and license for each cluster member. New installations and upgraded installations automatically receive a 3. Contact your Check Point representative to get full licenses and contracts. If you do not have a valid contract for a gateway, the Application Control blade is disabled. When contracts are about to expire or have already expired, you will see warnings.
Warnings appear in: The Message and Action item section of the Overview page of the Application Control tab. The Check Point User Center, when you log in to your account. Application Control Software Blade. The Application Control Software Blade is a Service Blade that requires annual renewal to enforce application control policy and to allow download of application updates from the Check Point Application Control Update Service. These updates enable you to recognize the most recent high risk applications, bandwidth consuming applications and more. The Application Control Software Blade verifies renewal information for every Security Gateway and disables Application Control functionality, if the Application Control contract is expired.
How to verify the status of Application Control contracts on all your Security Gateways. Each Security Gateway needs to be covered by an Application Control contract in order to use an Application Control Software Blade. The contract covers both applications that are provided out- of- the- box, as well as new applications, downloaded from the Check Point Application Control Update Service. The Application Control contract covers all applications of the Application Control Software Blade. Without a valid Application Control contract, the Security Gateway is not entitled to use any Application Control applications. There are 7 types of Application Control Software Blade contracts: CPSB- APCL- XL: Covers (ultra high- end appliances and software packages) 2.
Power- 1 1. 10. 00, IP 2. SG1. 20. 1. CPSB- APCL- L: Covers (high- end appliances and software packages) Power- 1 5. Power- 1 9. 07. 0, IP 1. SG8. 01. CPSB- APCL- M: Covers most mid- sized appliances and software packages. CPSB- APCL- S: Covers 2. UTM- 1 1. 30, UTM- 1 2.
UTM- 1 5. 70 and SG1. CPSB- APCL- L- HA: Covers (high- end appliances and software packages) Power- 1 5. Power- 1 9. 07. 0, Power- 1 1.
IP 1. 20. 0, IP 2. SG8. 01 and SG1. 20. Each contract, including the Application Control Software Blade, must be attached to a Blade Container or, when using NGX licenses, to a valid gateway license.
When contracts are purchased, they appear in the relevant User Center account. To verify if the Security Gateway has a valid Application Control contract: Go to the . Look for the Security Gateway's Container in the Product column, e. Click the link to open the Product Information Page. When you click on a container, you will be able to see the contracts associated with it. In the Product Information tab, check if an Application Control blade is attached to the Container.
The attached Application Control blade can be either a Built- in Blade or an Additional Blade. Built- in Blades: are purchased as part of a predefined Software Blades system. They have a lock displayed. Additional Blades: are purchased on their own, not as part of a predefined Software Blade system. They do not have a lock displayed. Look for the Support Renewal, to see if the Security Gateway is covered by the Application Control Service. Evaluation Contracts.
New installations and upgraded installations automatically receive a 3. Contact your Check Point representative to get additional evaluation licenses and contracts. For more information, refer to sk. How to check if the security gateway is covered by an IPS or Smart. Defense contract in User Center. Notifications about insufficient contract coverage. Smart. Update: You can check the complete license and contract coverage status via Smart.
Update. For more information, refer to sk. IPS Software Blade contracts in R7. Application Control Overview page: (added in R7. The Overview page of the Smart. Dashboard Application Control tab includes the Messages and Action Items section. This section shows an alert when a gateway has invalid, or insufficient Application Control contract coverage. A different warning appears when contracts are about to expire.
Application Control System Logs: (added in R7. The System log query of the Smart. View Tracker Application Control Blade sub- tree shows Application Control update related logs.
When a contract is expired, or about to expire, additional information is shown in the log description, describing the contract status. Contract Expiration window: (added in R7. During policy installation, the Contract Expiration window shows alerts with contract statuses. What happens when there is no Application Control contract. You must have an Application Control Software Blade contract to use the Application Control Software Blade functionality on a gateway. If a valid Application Control contract is not associated with a gateway, the blade will be disabled. When this change in functionality occurs, customers will be notified by: A pop- up warning message that appears on the screen, during policy installation.
An audit log that is sent periodically, notifying that the Application Control Blade is disabled. Once you purchase a valid contract, the blade is enabled again. Important: When an Application Control Blade is disabled due to insufficient contract, all Application Control settings in Smart. Dashboard do not change. The blade will appear to be active in Smart. Dashboard; however it will not be active on the gateway. New Installation or Upgrade of R7.
A new or an upgraded R7. Security Gateway includes a special trial license. This license allows all Application Control functionality for 3. The only licensing difference between an upgrade and a new installation is that in a new installation, a Plug and Play license is granted for 1.
Application Control blade is deployed on the gateway. After the trial license expires, the Application Control Blade is disabled. When using Evaluation Contracts. The Application Control Software Blade can be evaluated for 3. Evaluation contracts are treated the same as . When the evaluation contract expires, the Application Control Blade is disabled.
Grace Period. The grace period is the time period after the Application Control Blade license expires, during which the blade will still be active and no restrictions are made. However, warnings are issued regarding the missing contracts. The grace period is granted only after a . The grace period is set for 9. The grace periods are calculated per gateway, individually. FAQShow All. How is the contract information updated?
When purchasing a new Application Control Blade contract, the contract is added to your User Center account. In most cases, the contract will already be associated to a container (e. If this is not the case, you need to manually associate it (For more information, refer to sk. How to check if the security gateway is covered by an IPS or Smart.
Defense contract in User Center). On the Security Gateway, a task that runs every 2 hours updates the license and contract information from the User Center account to the Security Gateway.
Check Point 1. 12. Appliance . Built on the Software Blades Architecture, the 1. Appliance offers the same enterprise- class Check Point security that is used by all of the Fortune 1. Key Features. Software blades architecture on a small form- factor. Gb. E ports, ADSL and 3. G support. Local and Central management options.
Performance. Security. Power: 2. 8Firewall Throughput: 7. Mbps. IPS Throughput: 7. Mbps (Default)/ 1. Mbps (Recommended)Your Challenge. In the age of global business and increasingly more distributed workforce, remote and branch staff demand access to corporate resources in order to work effectively and efficiently. However, even a small data breach can expose growing companies to crippling lawsuits, penalties and loss of reputation.
As hacking techniques and malware evolve, the threat of data loss compels companies to further restrict access to sensitive data. With limited IT budgets and resources, branch offices need an inexpensive, yet effective solution to provide secure access to critical resources from anywhere, while minimizing the risk of a data breach. Our Solution. The Check Point 1. Appliances are a simple, affordable and easy to deploy all- in- one solutions for delivering industry leading security to protect the weakest link in your enterprise network—the remote branch offices. Protect against cyber threats with Check Point Threat Prevention Software Blades.
The Check Point 1. Appliance is an all- in- one, centrally managed, security appliance for branch offices and remote sites. Built on the Software Blades Architecture, the 1. Appliance offers the same enterprise- class security used by all Fortune 1.
The 1. 10. 0 Appliances, available in 3 models to match the number of users protected, are ideal for small offices with from one to fifty employees. A wide variety of network interface options are available including 1. Gb. E Ethernet ports, 8. Wi. Fi, ADSL and 3. G wireless connections.
These compact desktop appliances deliver outstanding performance of 1. Gbps firewall and 2. Mbps of VPN throughput. For local management and support in a small office environment, an easy and intuitive web- based local management interface is available. Os X Login Script Active Directory more. Enterprises who want to manage security from a central office can leverage Check Point Security Management or Multi- Domain Security Management to remotely manage and apply a consistent security policy to hundreds of devices across the field offices. Features. Software Blade architecture in a small form- factor New hardware optimized to address branch office network needs.
Flexible management options Benefits. Multi- layered protection against today’s sophisticated cyber- threats. Multiple network interfaces with optional wireless connectivity and ADSL connectivity to support any network deployment Multiple management options to address any organization’s needs- Simplified web- based Local Management- Centralized with Check Point Security Management. Key Features: Enterprise Security in a Small Form- factor.
Best- in- class Integrated Firewall and IPS 1. Appliances include the industry’s most proven firewall technology, based on the same Check Point technology that secures the Fortune 1. Together with Check Point’s proven IPS (rated “Recommend” by NSS); the 1. Appliance ensures protection of remote sites from both known and unknown threats. Next Generation Firewall Capabilities. Check Point’s Application Control and URL Filtering Software Blades unify web site access control with application control for improved security and lower cost.
Identify, allow, block or limit the use of thousands of applications, including Web 2. Combined with the Identity Awareness Software Blade, administrators can create granular policies to strike a balance between user application usage and security, productivity and resource utilization. Secure Connectivity Ensure secure communications between site- to- site and remote users with IPsec and SSL VPN.
Offering multiple connectivity methods (including Check Point’s VPN clients, SSL and mobile clients), The 1. Appliances ensures secure connectivity wherever you go. VPN Configuration for 1. Appliance. Anti- Malware Dynamic Protection The 1. Appliance’s enhanced Antivirus Software Blade uses real- time virus signatures and anomaly- based protections from Threat.
Cloud. The setup wizard enables a pre- set security policy. Customize the device configuration and security policy with the web- based management interface. Monitor the device and security with easy- to- understand logs and reports. Easy and Intuitive Local Management. Central Management Administrators can define security policy for the entire network—including internal security, main sites, and remote sites—from a single, centrally located Check Point Security Management server. With Smart. Provisioning. The optional integrated ADSL modem eliminates the need for a separate external ADSL modem.
Appliances also include a USB and PCI Express card slot that allows administrators to plug in a compatible third party 3. G modem, providing an additional WAN connectivity or a redundant Internet link for maximum reliability. Secure Wireless Connectivity The 1. Wireless Appliances include a WIFI access point (8. WEP, WPA and WPA2 authentication. Embedded GAi. A—The Unified Security OS Check Point GAi. A. GAi. A combines the best features from IPSO and Secure.
Platform into a single unified OS providing greater efficiency and robust performance. GAi. A secures IPv.
IPv. 6 networks supporting complex network environments by supporting dynamic routing protocols like RIP, OSPF, BGP, PIM (sparse and dense mode) and IGMP. Technical Specifications: 1. Security. Power. 28. Firewall Throughput (Mbps)Up to 3. Firewall and IPS Throughput (Mbps)Up to 3.
Recommended Users. Up to 1. 0Up to 2.
Up to 5. 0Firewall, 1. UDP (Mbps)7. 50. 1,0. VPN, AES- 1. 28 (Mbps)1. IPsec VPN Tunnels. IPS (Mbps)5. 06. 71. Antivirus (Mbps)5. Connections per Second, 6.
HTTP response. 5,0. Concurrent Connections, 6. HTTP response. 20. Gb. E LAN Interface.
Gb. E WAN Interface. Gb. E DMZ Interface.
ADSL Model. Optional. Optional. Optional. Wireless. Optional. Optional. Optional. G Modem Support. Yes.
Yes. Yes. USB Ports. PCI Express Slot.
SD Memory Card Slot. Enclosure. Desktop.
Desktop. Desktop. Dimensions Wx. Dx. H (Standard)2. 2 x 4. Dimensions Wx. Dx. H (Metric)8. 7. 5 x 1. Weight. 1. 2 kg (2. AC Input. 11. 0 – 2.
VAC, 5. 0 – 6. 0 Hz. Power Supply Rating.
A DC 2. 4W (Wired Models)1. A DC 2. 4W (ADSL & Wireless Models)Power Consumption (Max)1. WThermal Input (Max)5. BTUSafety. UL/c- UL 6.
The rack mount kit makes these Check Point models fit in a 1. The RM- CP- T1 has all the network connections from the rear on the front panel. The unit is 1. 3. U high. The total height is 2. U with the additional supplied front plate.
The RM- CP- T1 model is delivered in RAL 9. Black). Other colours can be delivered on project basis. 25 Product Key For Microsoft Word 2010.
Specifications. Color. RAL 9. 00. 5 Jet Black.
Height. 1. 3. U2. U with the additional supplied front plate. Dimensions(height x width x depth)5. Number of connections brought to the front. Console port to the front. Yes. Cables. 11x 0.
Couplers. 11x RJ4. Supported Models- Check Point 6. Check Point 1. 10. What's in the box- 1x CP- Rack + RJ4. Cables - Assembly materials- Installation guide.
EAN8. 71. 88. 68. UPC8. 52. 75. 40.